The Killer Code Series™ – Module 1: Power and Control
This 4-hour course, offered in-person or online, equips law enforcement, investigators, mental health professionals, and civilians to understand how power and control drive violent behavior.
Participants learn to recognize early warning signs, map operational codes, and apply the Operational Code of Sex & Violence™ to real-world cases. The course goes beyond prevention—showing how these insights can inform cold-case investigations, anticipate future crimes, and develop actionable intervention strategies. Through interactive exercises and practical tools, attendees gain the skills and resources needed to enhance situational awareness, mitigate high-risk scenarios, and strengthen both professional and community safety.
The Killer Code Series™ – Module 1: Power and Control
Duration: 4 Hours
Format: In-person or Online (Live or Webinar-Style)
Target Audience: Law Enforcement, Investigators, Threat Assessment Professionals,
Mental Health Professionals, First Responder Wellness Teams, Analysts, and Civilian
Professionals
Course Overview
Power and control represent one of the most consistent and behaviorally identifiable
motivations behind violent crime. Unlike impulsive violence, dominance-driven violence
is structured, progressive, and reinforced through behavioral rehearsal, coercive control,
and psychological entitlement.
This module explores how offenders use control as both a psychological
objective and an operational mechanism to shape victims, environments, and
outcomes. Participants will:
- Learn to identify early formation of dominance-based behavioral patterns
- Recognize escalation pathways
- Apply the Operational Code of Sex & Violence™ to detect risk before violence
occurs
Through operational code mapping, forensic case analysis, and escalation
modeling, attendees will develop the ability to identify control-motivated offenders
across domestic, occupational, and institutional settings.
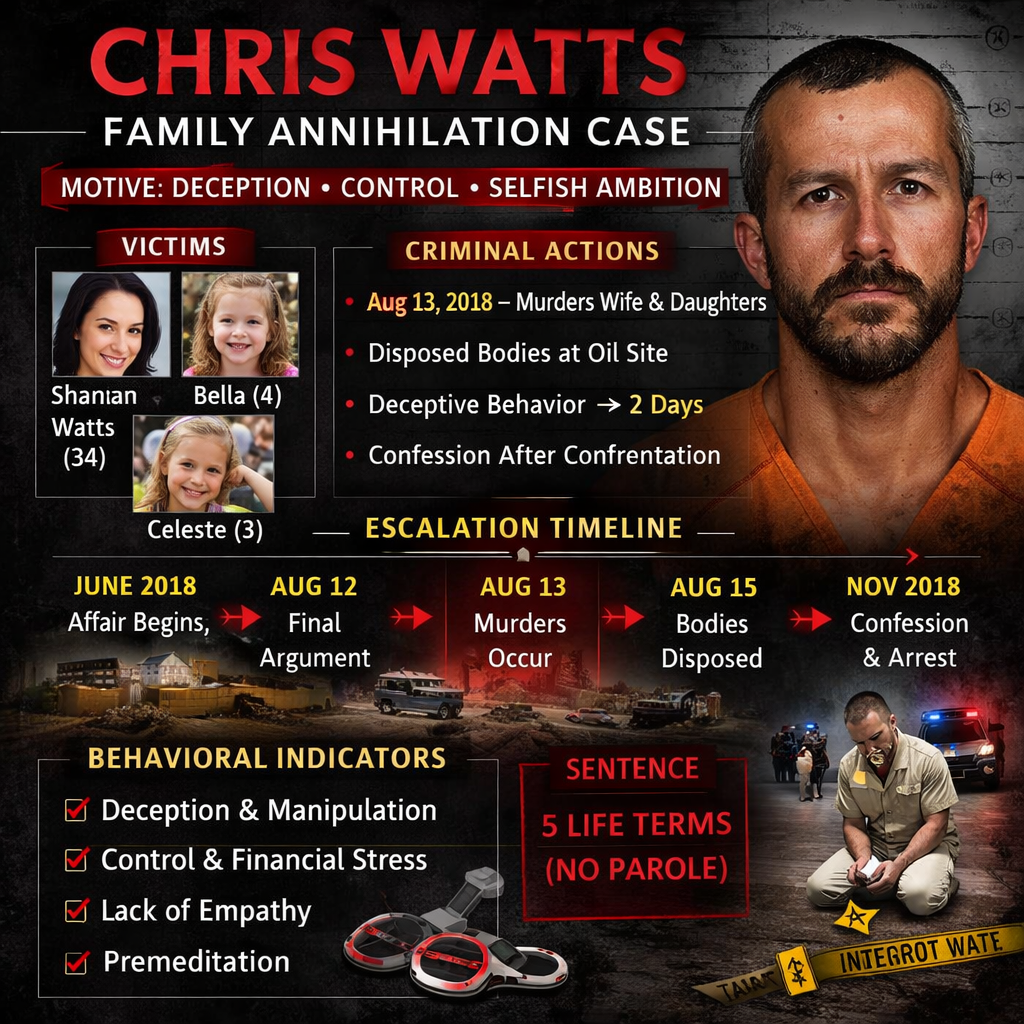
A detailed behavioral case study of Chris Watts, classified as a family annihilator, will
illustrate the intersection of coercive control, identity preservation, image management,
and elimination of perceived obstacles.
Outcome: Participants will leave with applied investigative frameworks, behavioral
detection tools, and prevention strategies designed to identify control-driven violence
during early escalation phases.
Learning Objectives
By the end of this module, participants will be able to:
1. Define power and control as primary operational drivers of violent behavior.
2. Identify behavioral indicators associated with coercive control and dominance-
based escalation.
3. Recognize early warning signs in domestic, workplace, and institutional
environments.
4. Apply the Operational Code of Sex & Violence™ to map offender motivation,
escalation, and execution.
5. Identify intervention opportunities during pre-violence escalation stages.
6. Distinguish family annihilators, domestic control offenders, and institutional
dominance offenders.
7. Develop prevention and intervention strategies based on observable behavioral
indicators.
8. Apply operational code mapping to investigative and analytical work.
Agenda and Time Breakdown
Time Topic Instructional Method
30 min Foundations of Power and Control Lecture
45 min Psychological Drivers of Dominance Lecture + Behavioral Analysis
45 min Behavioral Indicators and Escalation Patterns Case Study + Workbook
Exercise
60 min Case Study: Chris Watts – Family Annihilator Operational Code Mapping
30 min Operational Code of Sex & Violence™ Lecture + Applied Exercise
45 min Intervention and Prevention Strategies Applied Intervention Framework
15 min Summary, Competency Review, and
Reflection Guided Discussion
Course Content
Section 1: Foundations of Power and Control (30 minutes)
Definition and Operational Framework
Power and control-motivated violence is characterized by:
Desire to dominate another individual psychologically or physically
Preservation of identity, reputation, or authority
Elimination of perceived threats to control
Instrumental use of violence to restore or maintain power
Control-motivated offenders do not view victims as autonomous; they are seen
as extensions of identity, assets, or obstacles.
Core Operational Characteristics
Control-motivated offenders demonstrate:
Entitlement thinking
Possessiveness
Emotional detachment during escalation
Strategic deception
Maintenance of a double life
Workbook Exercise: Participants identify examples of control-based behavior in
professional, investigative, or personal environments and classify the escalation stage.
Section 2: Psychological Drivers of Dominance (45 minutes)
Primary Psychological Mechanisms:
Narcissistic identity preservation
Fear of exposure or loss of status
Ownership perception over others
Emotional detachment
Image management prioritized over human life
Loss of control produces escalation; control offenders seek outcome certainty.
Behavioral Indicators of Control-Motivated Offenders:
Early: Monitoring partner behavior, emotional detachment, secret relationships,
identity compartmentalization
Mid-Stage: Increased deception, withdrawal from family, financial manipulation,
emotional disengagement
Late-Stage: Sudden behavioral calmness, narrative rehearsal, pre-incident
planning
Workbook Exercise: Classify behavioral indicators into escalation stages.
Section 3: Behavioral Indicators and Escalation Patterns (45 minutes)
Operational Code Escalation Model:
Control-motivated violence follows identifiable stages:
1. Identity Threat
2. Narrative Construction
3. Behavioral Withdrawal
4. Target Dehumanization
5. Operational Planning
6. Violence Execution
Workbook Exercise: Analyze behavioral timelines from real investigative cases and
identify escalation progression.
Section 4: Case Study – Chris Watts: Family Annihilator (60 minutes)
Offender Classification: Family Annihilator – murders family members to eliminate
obstacles to identity preservation, financial freedom, or lifestyle change.
Background:
Chris Watts murdered his pregnant wife and two daughters.
Motivations: Desire to maintain extramarital relationship, financial pressure,
identity reconstruction, and removal of responsibility.
Operational Code Mapping:
Stage Trigger / Indicators Behavioral Patterns
1. Identity
Conflict
Extramarital relationship,
desire for new identity
Emotional withdrawal, secrecy,
detachment
2. Narrative
Formation
Family perceived as
obstacle
Lack of responsiveness, increased
deception, psychological distancing
3. Behavioral
Escalation
Financial concealment, affair
concealment
Operational shift from emotional conflict
to logistical planning
4. Execution Murder of wife and children Controlled, quiet, efficient, emotionally
detached
5. Post-Incident Media engagement, false
emotional displays
Narrative manipulation, calm
presentation
Workbook Exercise: Complete structured mapping: Motivation → Trigger → Escalation
→ Execution → Outcome.
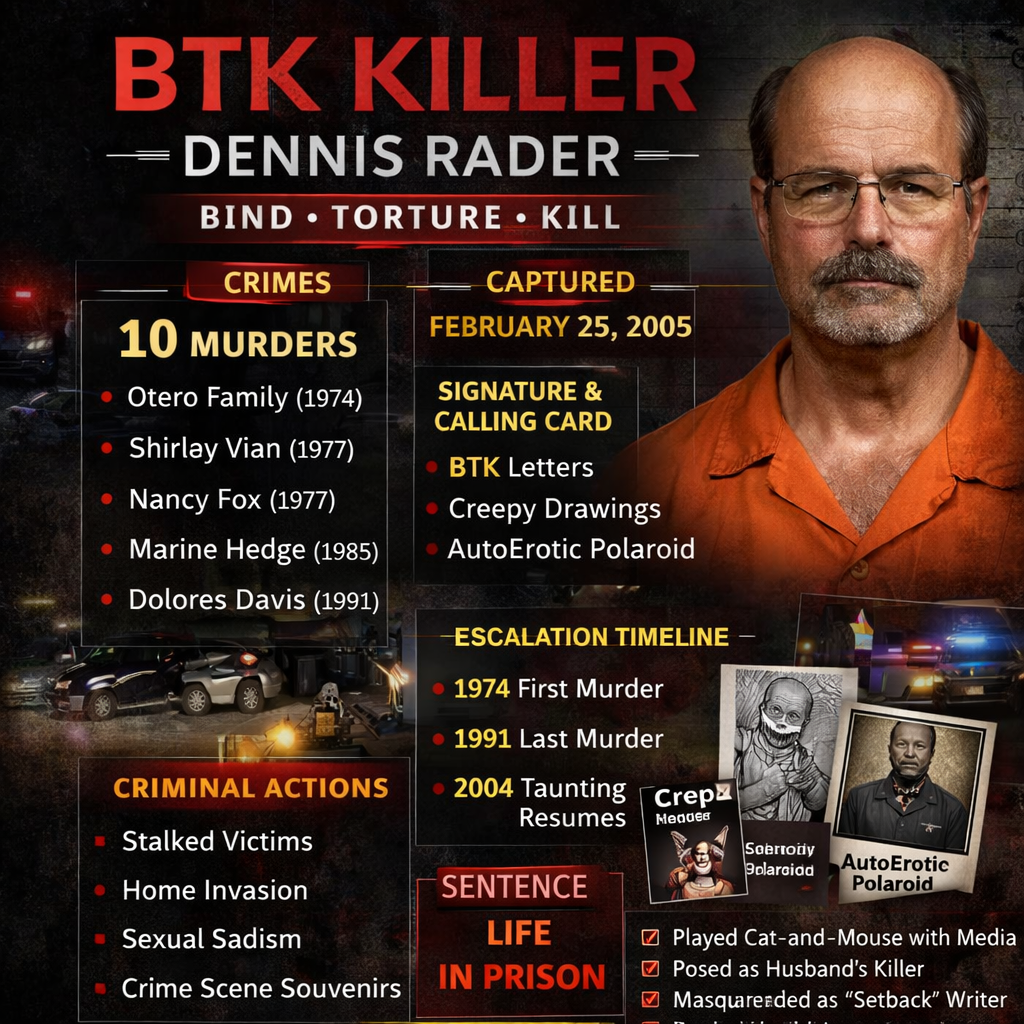
Section 5: Operational Code of Sex & Violence™ (30 minutes)
Definition:
The Operational Code of Sex & Violence™ is a structured analytical framework for
understanding the intersection of sexual motivation, dominance, and lethal behavior. It
enables investigators and threat analysts to:
Map offender motives (sexual, dominance, financial, psychological)
Identify triggers and escalation stages
Predict execution patterns
Determine intervention points
Components:
1. Motivational Axis: Desire for control, sexual gratification, or identity preservation
2. Escalation Axis: Early monitoring → Mid-stage deception → Late-stage
operational planning
3. Behavioral Signature: Rehearsed behavior, fantasy enactment,
compartmentalization
4. Execution Patterning: Instrumental vs impulsive, primary target vs collateral
victim
Applied Exercise: Participants review anonymized case vignettes and map the
offender’s Operational Code of Sex & Violence™.
Section 6: Intervention and Prevention Strategies (45 minutes)
Pre-execution detection is critical.
Stage-Based Intervention Opportunities:
Stage Indicators Intervention
1. Behavioral
Change
Withdrawal, secrecy, identity
conflict
Behavioral reporting, threat
assessment evaluation
2. Narrative
Escalation
Emotional detachment,
compartmentalization
Psychological assessment,
support intervention
3. Operational
Preparation
Sudden calmness, behavioral
finality
Immediate threat intervention, law
enforcement escalation
Workbook Exercise: Develop an intervention plan based on Watts escalation timeline.
Section 7: Capstone Project (Certification Requirement)
Objective: Apply the course framework to a real or historical case study.
Requirements:
Select one case from the module (Chris Watts or an alternative approved case).
Complete a written report including:
o Offender classification
o Identification of power/control motivations
o Operational Code Mapping (sex & violence axis)
o Escalation timeline
o Behavioral indicators
o Intervention points and prevention strategy
Minimum: 5 pages, APA style recommended
Submission required to earn Certificate of Completion
Evaluation Criteria:
Depth of behavioral analysis
Accuracy of Operational Code mapping
Clear identification of escalation stages
Practical recommendations for intervention and prevention
Section 8: Summary and Competency Integration (15 minutes)
Participants Review:
Behavioral indicators of control-motivated violence
Escalation timelines
Intervention points
Operational Code application
Workbook Reflection:
Three indicators I will recognize earlier
Three intervention strategies I will apply
One behavioral pattern I previously overlooked
Workbook Appendices / Tools Provided
Operational Code Mapping Sheet
Behavioral Escalation Timeline Template
Control-Based Violence Indicator Checklist
Intervention Planning Framework
Threat Assessment Worksheet
Behavioral Competencies Developed
Participants will be able to:
Identify dominance-driven offenders
Detect behavioral escalation patterns
Apply Operational Code analysis
Recognize family annihilator progression
Identify intervention opportunities before execution
Improve investigative and prevention outcomes
References
Canter, D. (2004). Offender profiling and investigative psychology.
Douglas, J. E., Burgess, A. W., Burgess, A. G., & Ressler, R. K. (2006). Crime
Classification Manual.
Ressler, R. K., Burgess, A. W., & Douglas, J. E. (1988). Sexual Homicide:
Patterns and Motives.
Wolfgang, M. E. (1958). Patterns in Criminal Homicide.
Meloy, J. R. (2000). The Psychology of Stalking and Threat Assessment.
Campbell, J. C. (2003). Risk Factors for Femicide.
Scheinin, L. (2019). Family Annihilators: The Psychology of Domestic Mass
Murder.
Fox, J. A., & Levin, J. (2015). Extreme Killing: Understanding Serial and Mass
Murder.
Holmes, R. M., & Holmes, S. T. (2009). Profiling Violent Crimes.

